EU Cyber Resilience Act (CRA)
The newly proposed EU Cyber Resilience Act is highly relevant for the Industrial Internet of Things (IIoT), Industrial Automation & Control Systems, and general-purpose microprocessors. It is driven by the enormous cost caused by cybercrime, estimated at EUR 5.5 trillion in 2021. The EU understands that this is caused by low cybersecurity standards in HW and SW and the inability of users to choose products with adequate security due to missing transparency. The penalties for non-compliance are up to €15 million or 2.5 percent of their global annual turnover.
Some of the Requirements for the Cyber Resilience Act
- Communication about vulnerabilities
- No delay in patching the vulnerabilities
- Secure-by-default configuration
- Cybersecurity risk assessment
- Software Bill of Material (SBOM) requirements

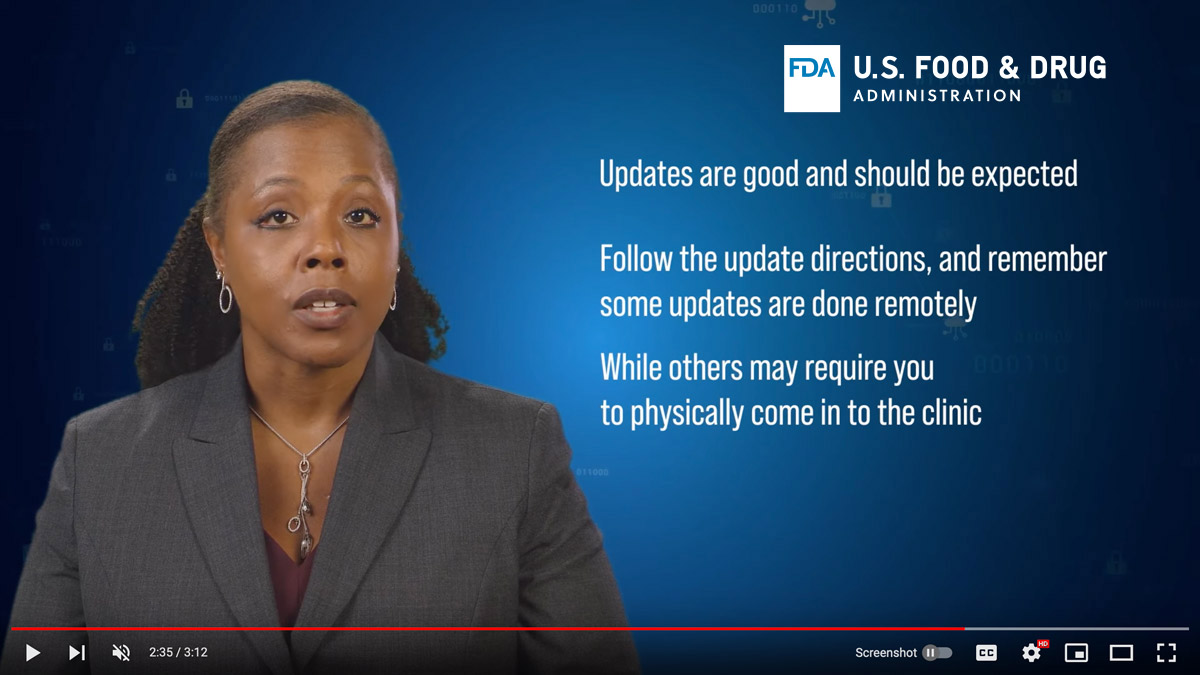
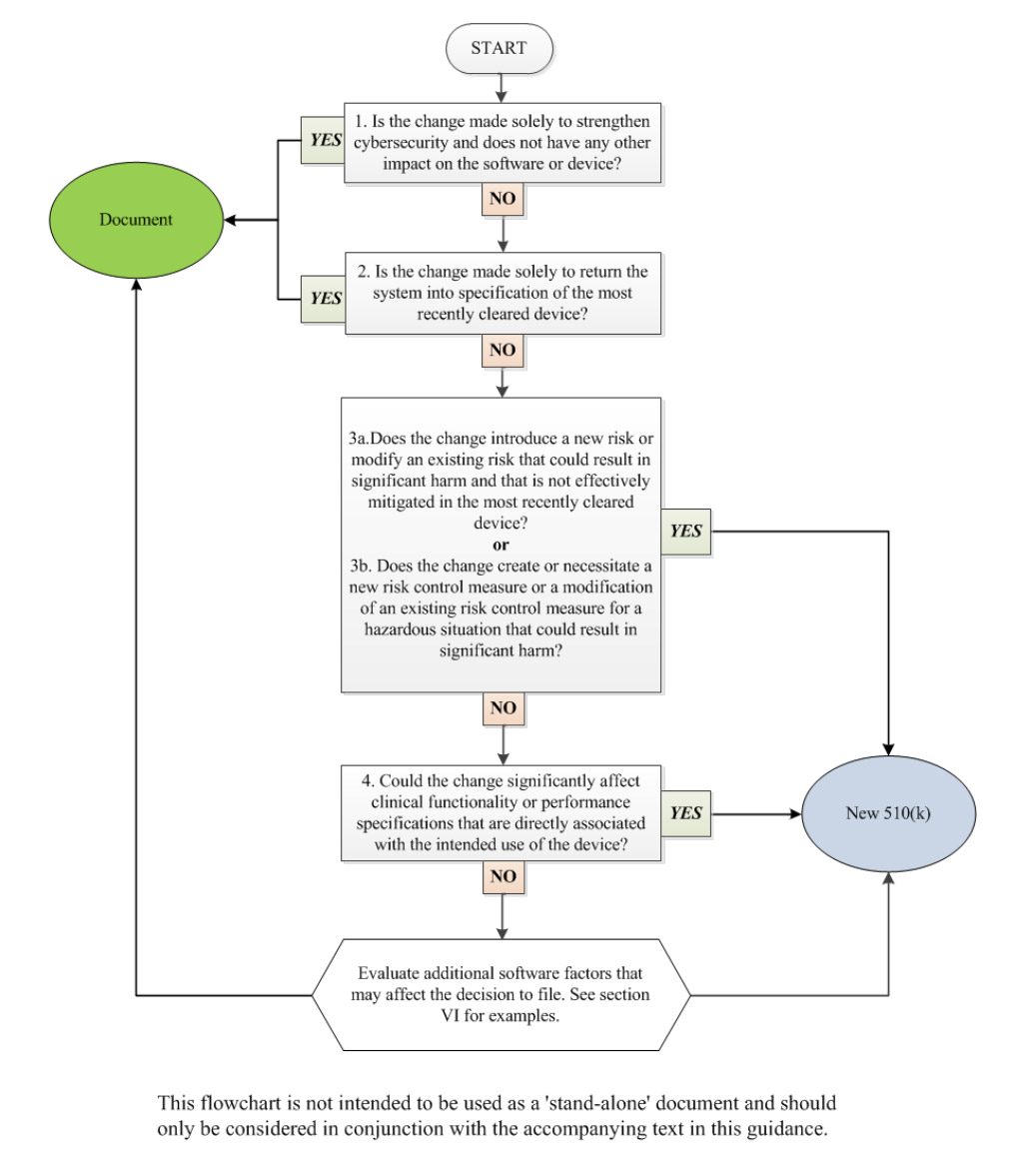
FDA- Software Updates are now expected
For a long time vendors of medical devices have tried to avoid changes to the HW or SW product to avoid needing recertification and a submission of 510(k). However, the requirements are changing. Now, companies are required to keep the software up to date and provide secure update functionality. Changes improving the cybersecurity of the device means it does not require a 510(k).
From the new Cybersecurity in Medical Devices: Quality System Considerations and Content of Premarket Submissions Draft Guidance for Industry and Food and Drug Administration Staff
On Software Updates
- Anticipate the need for software patches
- Consider the update process's reliability in the event of communication interruption or failure
- Implement processes for rapid verification, validation, and distribution of patches and updates
Whitepaper
Cybersecurity in Medical | Healthcare Devices - Evolving Regulations
How Torizon Helps
Reliable Updates Process
Proven Security Framework
Frequent OS Updates
Rapid development, testing and deployment
Integration with Secure Boot
Vulnerability Manager
Software Bill of Materials (SBOM)
Defense in Depth
Videos
How TI and Toradex streamline cybersecurity, usability and time to market
Discover how the partnership between Toradex and Texas Instruments (TI) boosts embedded Linux security and supports compliance with the EU Cyber Resilience Act (CRA) and the FDA cybersecurity guidance . Learn how Torizon OS enables secure, efficient development on Toradex SoMs like the Verdin AM62 and Aquila AM69, and how TI integrates Torizon OS into AM62x, AM62P, and AM67 BeagleY-AI starter kits, with broader support coming soon.
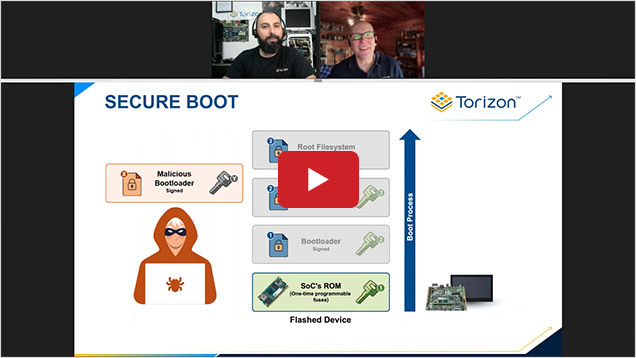
Out-Of-The-Box Secure Boot and Support with Torizon
Torizon now supports Raspberry Pi, generic x86, RISC-V, and many other platforms, providing more flexibility and options for developers! Discover how Torizon is leading the way with secure boot support on the Texas Instruments AM62 System on Module and what's next on the roadmap for enhanced security features.
Cybersecurity Compliance with Savoir-faire Linux and Torizon
Discover how Savoir-faire Linux is leveraging Torizon to facilitate secure boot, manage software vulnerabilities, and support a comprehensive Software Bill Of Materials (SBOM) to enhance security from the ground up for customers.
IoT Security Blog Series
IoT Security Blog Series Part 3
Software update security: Common mistakes
This is part 3 of our 7-part series about over-the-air software updates. In part 1, we told you about all the reasons it’s important to be able to deliver software updates remotely, and in part 2 we wrote about all the reasons software update systems are dangerous. Today, we’re looking at ways to protect your software update system that might seem secure at first glance, but aren't—with famous real-world failures for each example.
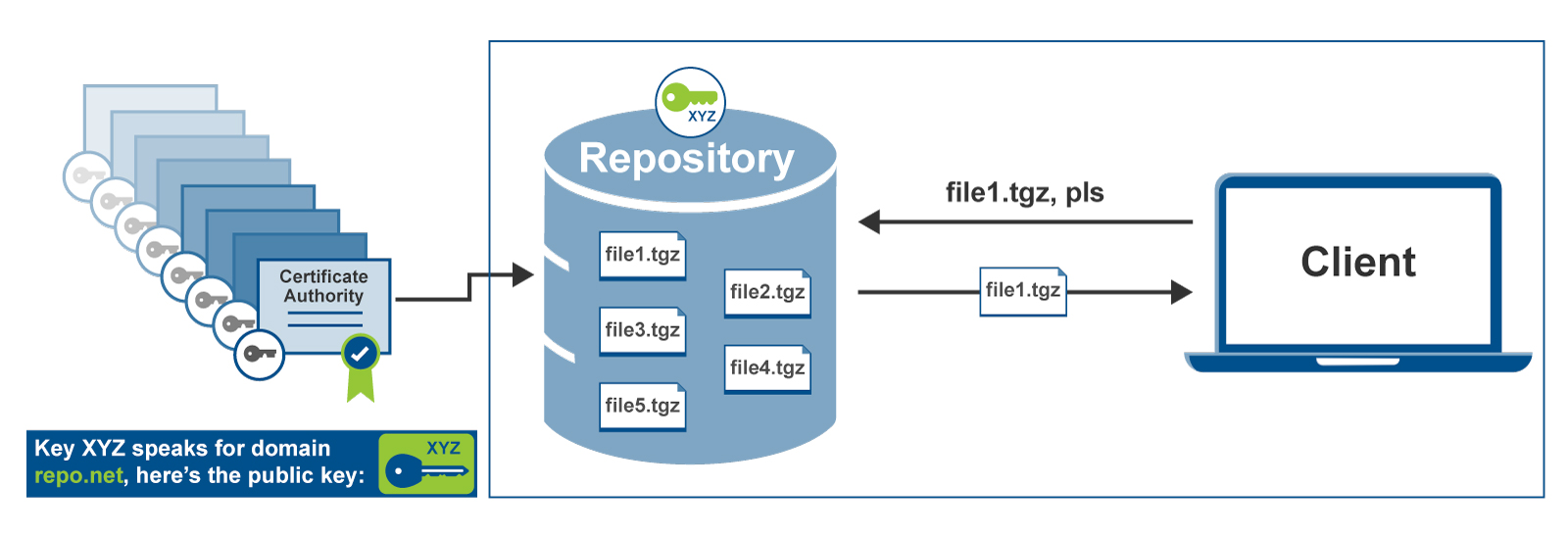
IoT Security Blog Series Part 2:
The dangers of remote updates
This is part 2 of our 7-part series about over-the-air software updates. In part 1, we told you about all the reasons it’s important to be able to deliver software updates remotely - in today’s world, you can’t keep any connected device secure unless you can update it. Today’s post, though, goes in the opposite direction: we’re going to look at why software update systems can be incredibly dangerous, and why you should treat them with skepticism and caution.
IoT Security Blog Series Part 1:
Why do we need remote updates for connected devices?
With the explosion of internet-connected devices in recent years, there has been an industry-wide realization of the need to keep these devices updated throughout their lifetime. This is the first part of a series that will explore the concept of remote over-the-air (OTA) updates, providing designers details they will need when implementing remote OTA update solutions into their systems. We will especially focus on the important security aspects. We’ll start with the basics.
On-Demand Webinars
Safeguard your Embedded Linux devices with Secure Boot
In this webinar, we will explain what Secure Boot is, why it’s needed, and how it’s implemented. We also present a live demo, illustrating how Toradex makes it easy to enable Secure Boot using the Yocto-based Linux Torizon OS.
Enhanced Cybersecurity and FIPS 140-2 Compliance using NXP® i.MX 8X
The road to cybersecurity compliance for regulated applications in the utilities, medical, and defense industries can be difficult. Achieving the required certifications can significantly increase timelines for development time/cost which can significantly delay a product launch.
Get Started
My team owns
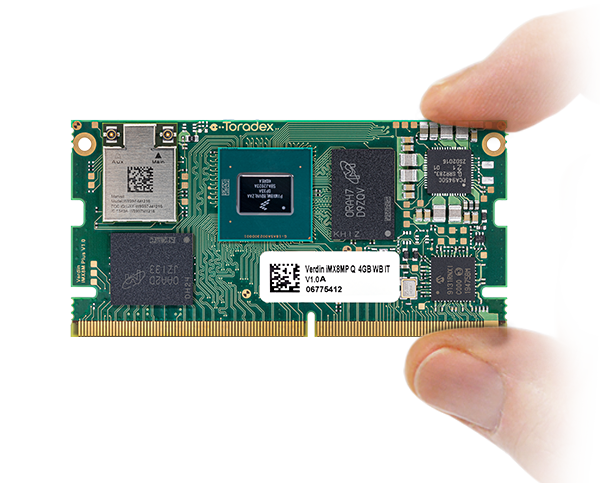
Torizon is fully integrated with Toradex Hardware
Torizon OS runs on most of our newer modules! Leverage a fully integrated stack and start developing today.

Integrating Torizon is easier than you think!
Torizon OS is fully Open Source! We provide references on how to integrate it with your own hardware. Do it yourself or with our partners!

We have everything you need to get started!
To kick-start your evaluation, choose from these Starter Kits to profit from the tight software-hardware integration.
Get in Touch With Us
Want to know more about Torizon?