
The blog posts give you an in-depth understanding of Torizon, its advantages, use cases, the latest updates, and developments.
As robotics grow more sophisticated, many developers are turning to frameworks that can handle increasingly complex robotics and automation tasks. ROS2 (Robotic Operating System) is a powerful middleware framework for building modular and scalable robotic applications due to its capabilities, support for distributed computing, and strong community.

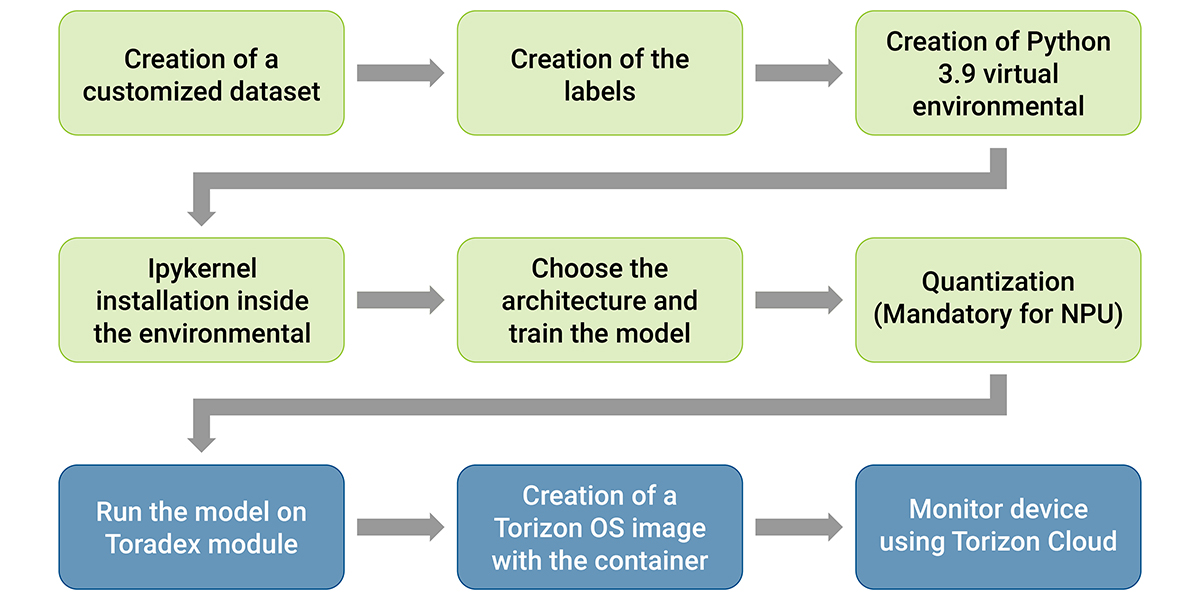
This project presents an end-to-end object detection AI, including training and model inference with hardware acceleration by Neural Processing Units (NPUs). This application will be done using a large video pipeline, which requires a computational system capable of processing camera images and performing AI inference.
With Torizon Minimal, Toradex removed the integration burden from you, so it helps you bring your Yocto-based product faster to the market and maintain it with a lower total cost of ownership, as you skip this costly integration and maintenance.

As of today, the Cyber Resilience Act (CRA) officially enters into force, ushering in new regulatory requirements for manufacturers of embedded devices and critical software. Although most provisions of the CRA won’t take effect until late 2027, it is critical for device makers to start preparing now.

In this blog post, we will explore how Torizon and Azure IoT complement each other, providing a seamless and powerful solution for a wide range of edge computing use cases.

Currently, two primary Linux OS Image update models are used in the embedded industry to perform OTA updates: Dual A-B Partitioning, and OSTree. In this blog, we’ll analyze the unique advantages of Torizon in challenging update scenarios.
Torizon has several security features that help you reach compliance with reduced effort and cost. Secure Boot is one of the pieces of the puzzle to becoming compliant, as it ensures only trusted software is executed during the boot.

In light of that, it's time to migrate, if you haven't already, to a new platform! But, you might be asking yourself: which one? And how?
Torizon team has worked to make the migration and learning curve as smooth as possible.
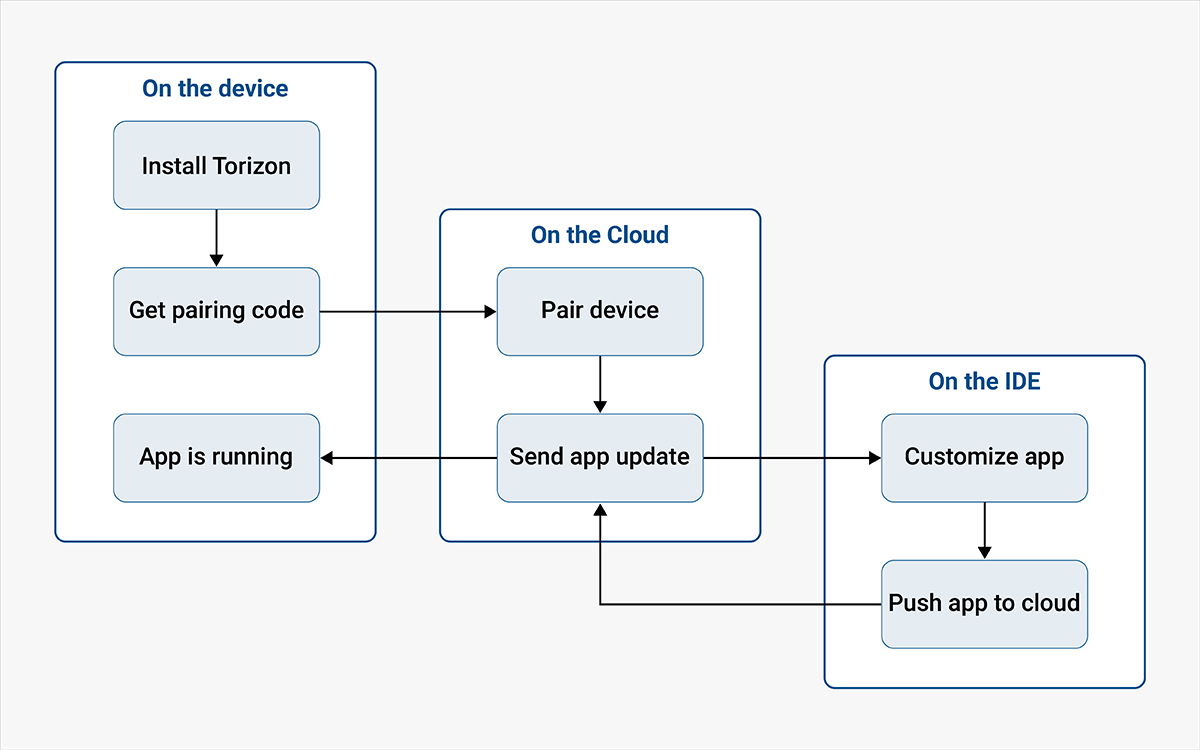
With the release of Torizon OS 6.6.1, the usual Portainer app has been replaced by Torizon Easy Pairing and it may have brought some questions on your side: why did we change it? Does it matter to you?
Torizon saves time and effort, you need not worry about picking an IDE or setting up an SDK. You need not have to abandon your Windows PC anymore, because Torizon supports it.

Torizon OS is an open-source, industrial, embedded Linux distribution with no vendor lock-in. Whether you seek community support or assistance from Toradex, transitioning from other providers like Foundries.io is seamless.
To many developers it is not clear how they can leverage Torizon Cloud in the development phase of a project. In this article we offer insights into how some of our customers are leveraging Torizon Cloud to make development both more efficient and more fun.
Torizon makes offline updates of embedded devices simple, safe, and reliable. In part two of our blog series on secure offline updates, we explore why it matters and how it works. Torizon’s secure offline update service for embedded Linux devices was developed from the ground up to de-risk software updates and make them hassle-free.

Developing Machine Learning applications often raises several questions. Edge Impulse provides a platform that simplifies ML application development at the edge. In this blog post, you will see how to build a classification model that distinguishes between three distinct objects.
Online update capability is establishing itself as the gold standard for state-of-the-art devices, for several reasons. The ability to issue updates from a centralized location reduces maintenance efforts (and CO2 emissions) associated with dispatching technicians to remote locations.

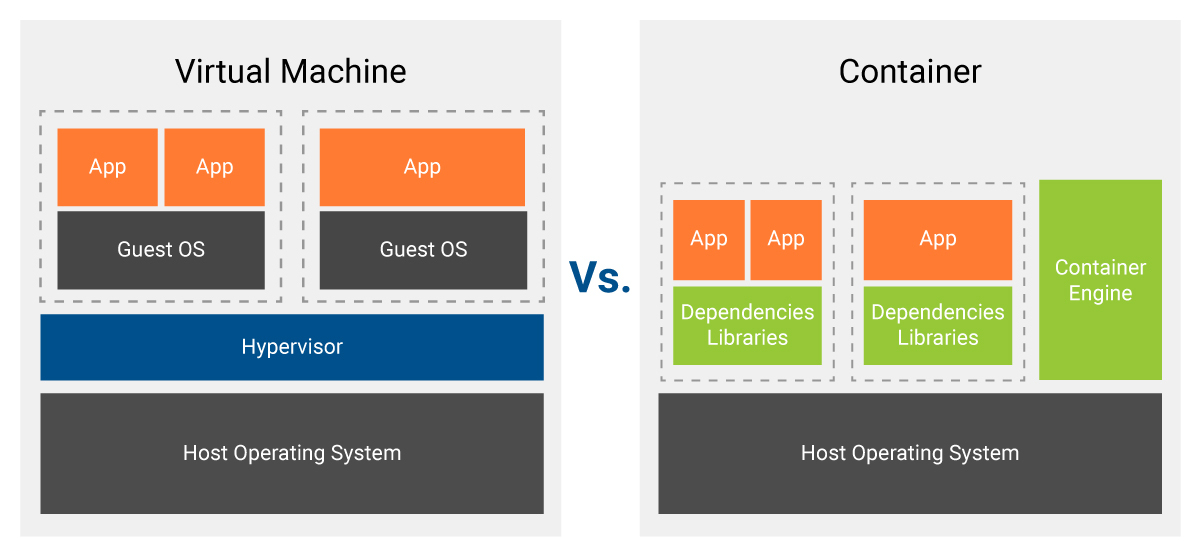
In this article, we will explore some of the variables, and highlight some common mistakes and the best practices for creating and developing your containers with performance in mind. The goal here is not to show if the same-performance premise actually reflects real-life applications, but instead to show how you can get the most out of your container to make the Docker overhead virtually nonexistent. Lastly, we will also showcase some possible issues that may arise when starting multiple containers at once and how all of this affects memory and boot time.
The quality of our hardware and software is well known, and we are committed to open-source initiatives in most projects across our product line. We are an active contributor to the Linux kernel in particular and, in keeping with this, recently changed our strategy to commit everything possible to the mainline Linux kernel — we are now enthusiastically "Upstream First."
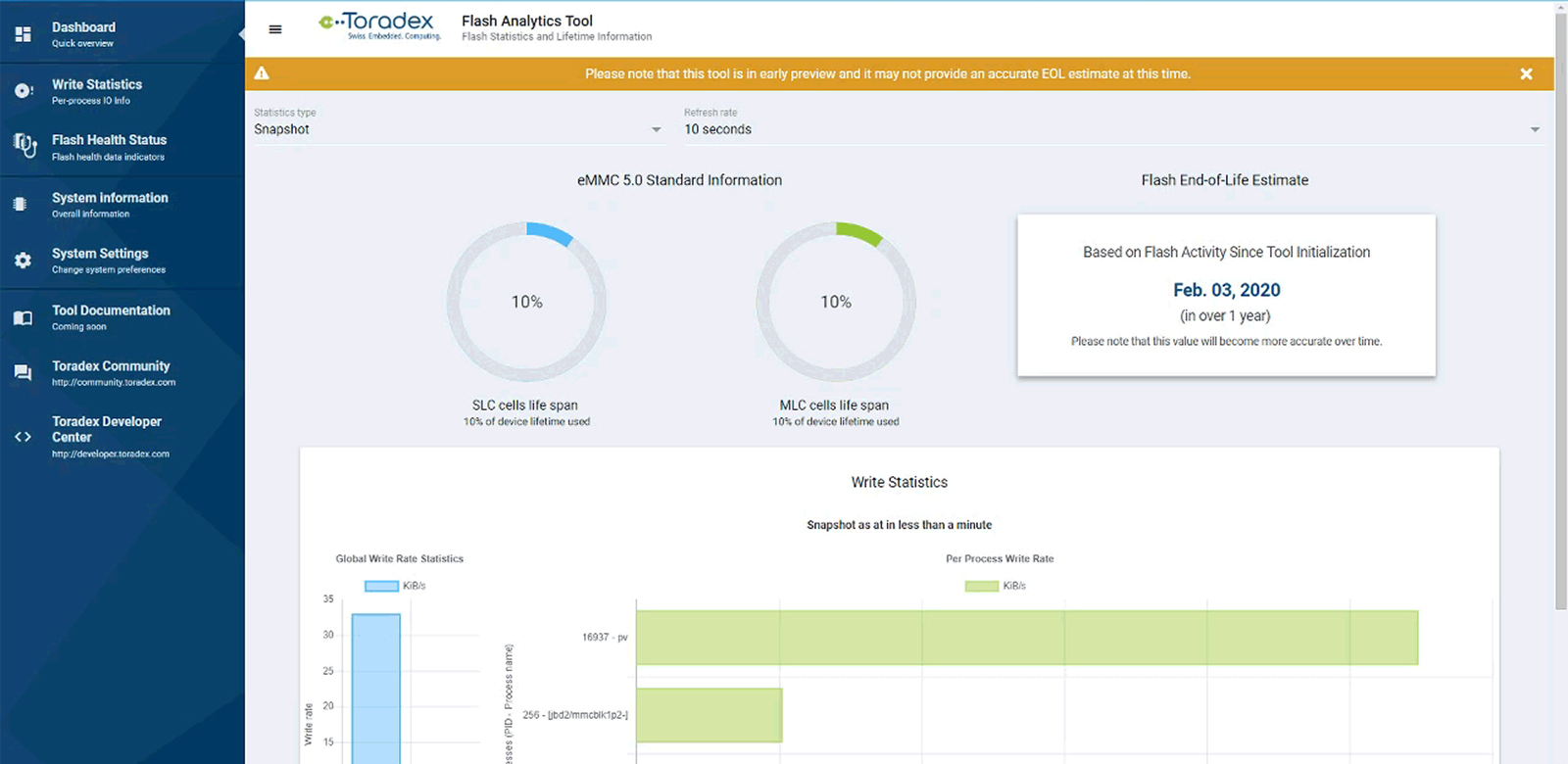
Hey there, Leo here! Some years ago, I worked on an innovation project - by now archived - named Flash Analytics Tool. One of the project goals was to research and apply methods to estimate flash memory lifespan on Embedded Linux - more specifically, using Torizon in its early days - thus helping our customers develop flash-friendly applications and get an estimate of how long they could expect their devices to withstand in the field.
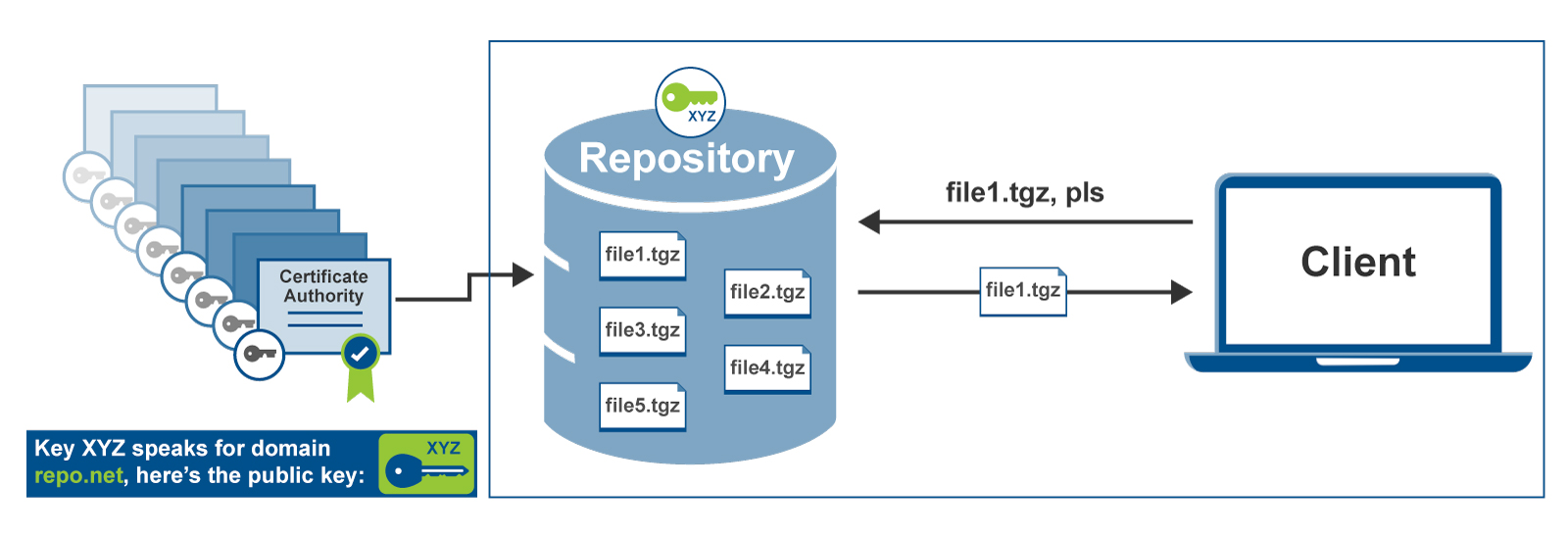
This is part 3 of our 7-part series about over-the-air software updates. In part 1, we told you about all the reasons it’s important to be able to deliver software updates remotely, and in part 2 we wrote about all the reasons software update systems are dangerous. Today, we’re looking at ways to protect your software update system that might seem secure at first glance, but aren't—with famous real-world failures for each example.
For some time already, Flutter has been quite successful as a native HMI and Application technology on the Web, Mobile Phones, and even for Desktop. Developers love the programming language, its performance, and the outstanding feature richness (e.g., the ability to create performant and custom animations of any complexity). It is extensively used by Google internally. Moreover, with its attractive BSD license, it has been used by many independent software development vendors meanwhile.


When project managers hear a project involves writing embedded software there is an expectation that a software developer with very specialized skills will be required to work on the project. Embedded software development historically requires a developer with both an electrical engineering and computer science background, writing software and firmware in a low-level language like C or C++, acquiring expensive software development tools, and typically the developed user interface will be rudimentary by modern GUI standards.

This is part 2 of our 7-part series about over-the-air software updates. In part 1, we told you about all the reasons it’s important to be able to deliver software updates remotely - in today’s world, you can’t keep any connected device secure unless you can update it. Today’s post, though, goes in the opposite direction: we’re going to look at why software update systems can be incredibly dangerous, and why you should treat them with skepticism and caution.
With the explosion of internet-connected devices in recent years, there has been an industry-wide realization of the need to keep these devices updated throughout their lifetime. This is the first part of a series that will explore the concept of remote over-the-air (OTA) updates, providing designers details they will need when implementing remote OTA update solutions into their systems. We will especially focus on the important security aspects. We’ll start with the basics.